
When code can black out a city and an algorithm can down a helicopter, the boundary between the digital world and physical war ceases to exist.
The technology has been the main driver in advancement of warfare from bronze swords to gunpowder, from the machine gun to the atom bomb. The emergence of Cyber-Physical Systems (CPS) technologies that seamlessly bridge digital computation and real-world physical action represents something qualitatively new. It is not just a new weapon; it is a whole new battlefield. Power grids that can be hacked into darkness, missiles guided by spoofed satellite signals, drone swarms commanded by artificial intelligence are not science fiction. They are today’s operational reality. For India, flanked by two nuclear-armed adversaries with proven offensive cyber capabilities, this reality demands a strategic response of the highest urgency.
It is in above backdrop this article maps the landscape of cyber-physical warfare, grounded in hard data analysis, examines India’s specific threat environment and current preparedness gaps, and charts, actionable way forward.
Where the Digital World Becomes Lethal

Imagine a morning when Mumbai’s financial district goes dark not because of a power cut, but because an adversary’s code has quietly reached into India’s electricity grid and issued the shutdown command. Imagine drones swarming over a forward operating base, not piloted by any human, but directed by an AI algorithm halfway across the world. Imagine a soldier’s GPS showing him ten kilometres from where he actually stands, courtesy of a spoofing signal from a hostile transmitter. None of this is imagination anymore, it is cyber-physical battlefield, and it is live.
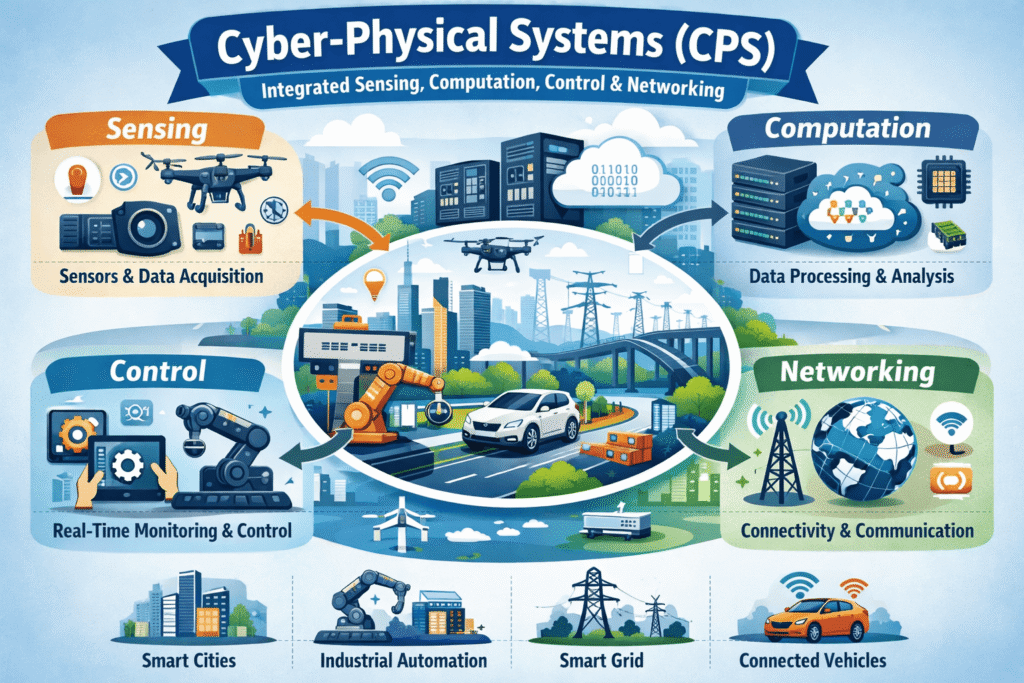
Cyber-Physical Systems (CPS) are defined as engineered systems that integrate sensing, computation, control, and networking into physical objects and infrastructure. In plain terms: systems software and hardware are so deeply intertwined that attacking one means attacking both. The global CPS market was valued at $87 billion in 2022 and is expected to surpass $137 billion by 2028 driven by defence, energy, transport, and telecommunications. Every dollar of that growth is simultaneously a dollar exacerbating national security risk, because every CPS is a system that can be turned against its owner.
The transformation is confirmed by the most dramatic illustration in recent memory: when coordinated U.S.-Israeli strikes hit Iranian targets on 28 February 2026, more than 60 Iranian-aligned hacktivist groups mobilised on Telegram within hours, targeting not military assets but power grids, water systems, and financial networks. This is the new playbook: kinetic strikes open the door; cyber-physical attacks exploit the chaos.
For India, one of the world’s five most cyber-breached nations the imperative has never been starker. In 2026, India faces an unprecedented “Cyber-storm,” with the World Economic Forum ranking cyber insecurity as a top five risk, requiring a shift from reactive to proactive defence together with AI-driven resilience. The battlefield is defined by 505+ malware detections per minute, AI-driven deepfakes, state-sponsored APTs targeting infrastructure, and the need for indigenous tech sovereignty.
Anatomy of the Cyber-Physical Battlefield

What Makes CPS Different and Deadly
Traditional cybersecurity is about protecting data confidential files, communications, financial records. CPS security is about protecting reality itself. When a CPS is compromised, the consequences are not a stolen password they are a breached dam, a derailed train, a targeted missile that strikes the wrong coordinates. The attack surface is no longer just servers and databases; it is power plants, pipelines, aircraft, and artillery.
The architecture of a CPS consists of five interlocking layers: physical processes (the real-world systems doing actual work), sensors (which observe and measure), communication networks (which transmit data), computational nodes (which process and decide), and actuators (which execute commands in the physical world). Compromise any layer and you compromise the whole system often with consequences that are simultaneously digital and devastatingly physical.
Stuxnet and the Birth of Kinetic Cyber
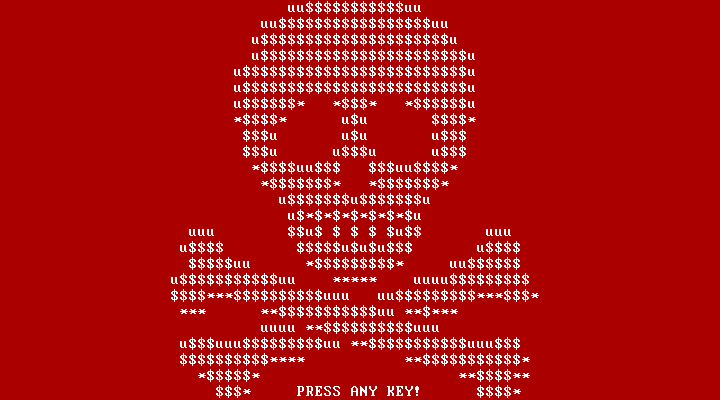
The proof of concept arrived in 2010 with Stuxnet jointly attributed to the United States and Israel which exploited vulnerabilities in Programmable Logic Controllers at Iran’s Natanz nuclear enrichment facility. The result: over a thousand centrifuges physically destroyed while their digital readouts showed normal operations. No bombs fell. No soldiers crossed a border. Code did what ordinance used to require. This was the moment cyber warfare grew a body the first confirmed kinetic cyber attack in history.
The global military CPS market: Numbers that reveal intent
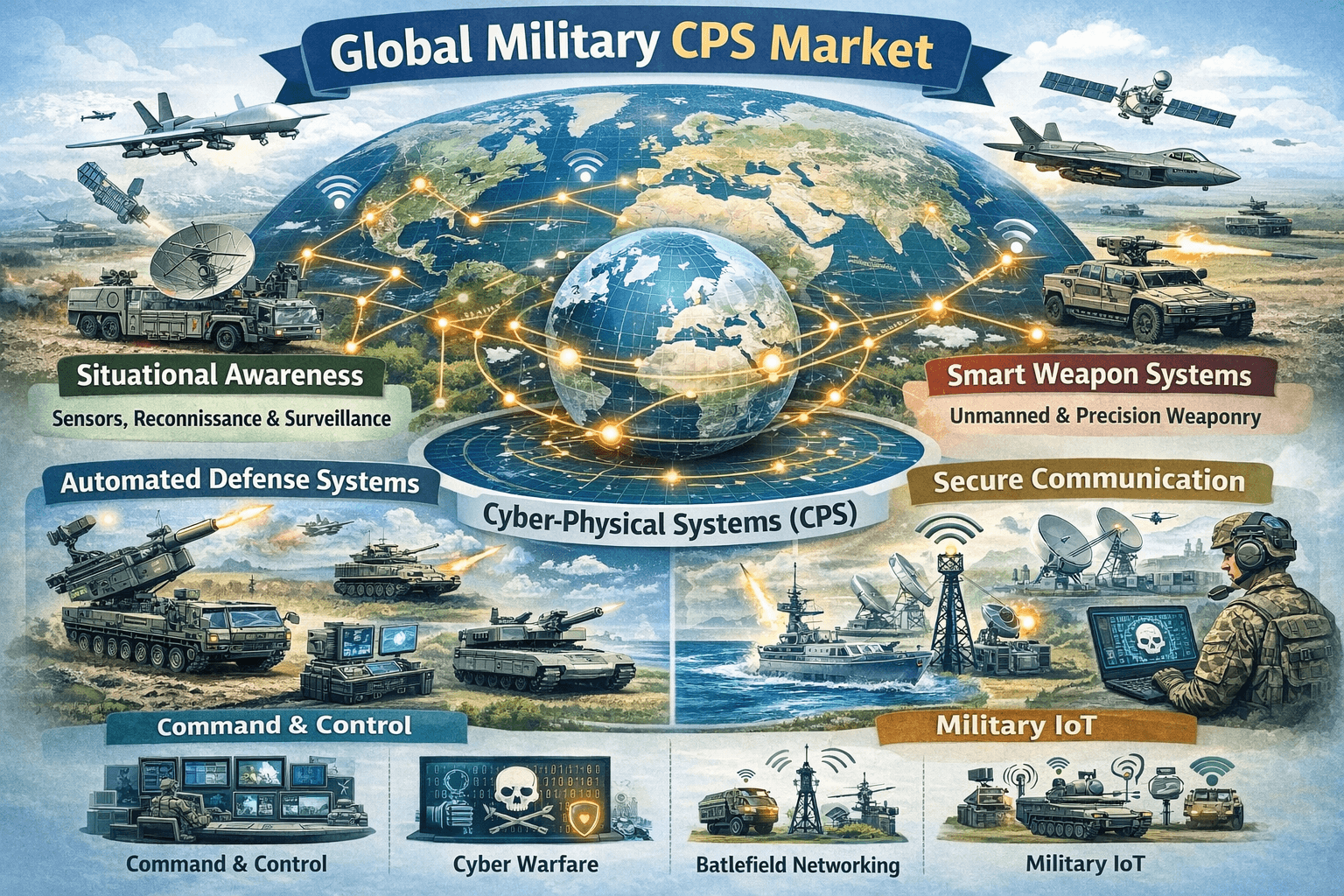
The scale of global investment in military CPS technologies is itself a strategic signal. Nations do not spend this money on capabilities they do not intend to use or fear will be used against them (Table 1):
Table 1: Global military CPS & related technology markets – scale & growth projection
| Domain / Market Segment | 2024 Value (USD) | Projected Value (USD) | CAGR (%) |
| Global Cyber-Physical Systems (CPS) | $87 Billion | $137 Billion (2028) | 7.9% |
| Military Drone / UAV Market | $15.23 Billion | $22.81 Billion (2030) | 7.6% |
| Electronic Warfare Systems | $18.6 Billion | $26.6 Billion (2034) | 5.2% |
| AI in Modern Warfare | $9.62 Billion | $28.82 Billion (2034) | 12.96% |
| Global Cybersecurity Market | $190 Billion | $299 Billion (2030) | ~8% |
(Sources: Markets and Markets, Globe Newswire, Market Research Future, Splunk (2023–2025)
These figures reveal a world engaged in a quiet arms race not of tanks and artillery, but of algorithms and autonomous systems. The country that masters this race will define the military balance of power for the next half-century.
Battlefield in practice: lessons from recent conflicts
Russia-Ukraine: The World’s First Full-Spectrum Cyber-Physical War
The Russo-Ukrainian War is the most comprehensive live laboratory for cyber-physical warfare that history has produced. Russia’s strategy has been nothing less than a systematic assault on the cyber-physical architecture of Ukrainian civilization the power that warms homes, the communications that coordinate defence, the satellites that guide soldiers.
Russia’s attacks on Ukraine’s power grid in 2015 and 2016 using malware targeting industrial control systems were the opening act. In 2022, the Viasat satellite attack disrupted Ukrainian command-and-control in the critical first hours of the full invasion a cyber-physical strike of enormous strategic consequence. Ukraine’s CERT-UA processed nearly 6,000 cyber incidents in 2025, with hostile attacks rising 37% year-on-year.
Ukraine’s response rewrote the doctrine of the underdog. Facing a far larger adversary, Ukrainian forces innovated with cheap, lethal, autonomous CPS tools. In July 2024, a Ukrainian operator used a commercial drone costing a fraction of its target to destroy a Russian Mi-8 helicopter. The lesson for India is powerful: in cyber-physical warfare, ingenuity and asymmetric tools can offset conventional disadvantage.
Operation Sindoor and the Cyber Dimension of Warfare

India’s Operation Sindoor in May 2025 marked a watershed in South Asian military history. India employed Rafale jets carrying SCALP missiles, AASM Hammer glide bombs, and BrahMos cruise missiles alongside Israeli-origin SkyStriker loitering munitions, striking targets in Pakistan and Pakistan-Occupied Kashmir with precision and without crossing into Pakistani airspace. These standoff, CPS-guided weapons executed a mission that in an earlier era would have required a full air campaign.
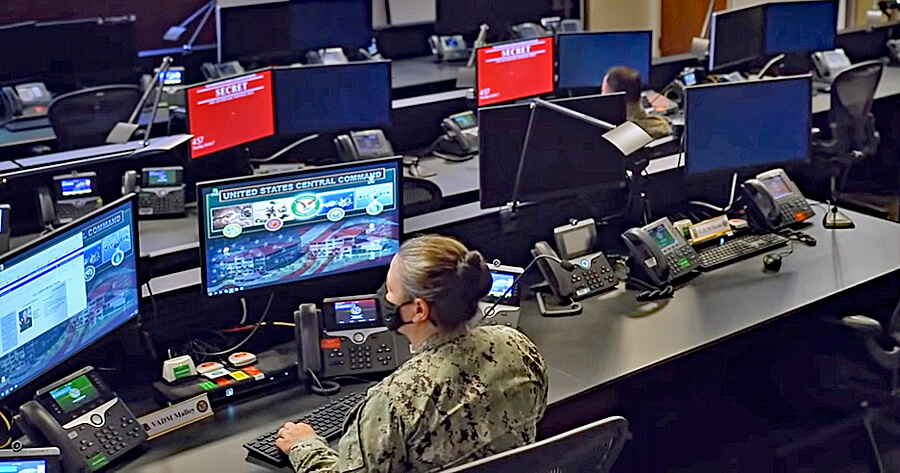
But what followed on the cyber front revealed an equally significant dimension. Within hours of Operation Sindoor, India’s national power grid faced approximately 2,00,000 attack and probing attempts. The President’s official website suffered a DDoS attack lasting nearly 19 hours. Seven APT groups mounted over 15 lakh cyber attacks on India’s critical information infrastructure a simultaneous cyber-physical assault timed to the kinetic operation. This was not coincidence. It was coordinated hybrid warfare.
The Iran-Israel Conflict : Fusion of Kinetic and Cyber Operations

The 2025-26 Israel-Iran conflict has demonstrated the most sophisticated fusion of kinetic and cyber-physical operations to date. Israeli forces conducted over 200 airstrikes using more than 330 munitions against approximately 100 Iranian targets each guided by CPS-dependent targeting systems while Mossad operations simultaneously disabled Iranian air defences through what analysts described as ‘electronic and cyber preparation of the battlefield.’ The lesson: in modern conflict, there is no longer a distinct ‘cyber phase’ and a ‘kinetic phase.’
Three Pillars of Cyber-Physical Warfare
Autonomous Drones and Swarm Intelligence

The drone has become the defining weapon of the cyber-physical age. Low-cost, GPS-guided, AI-directed, and proliferating globally, drones have compressed the distance between a software command and physical destruction to near zero. The global military UAV market is expected to grow from $15.23 billion in 2024 to $22.81 billion by 2030 (CAGR 7.6%), driven by the integration of AI into autonomous targeting, obstacle avoidance, and swarm coordination.
China’s drone programmes including bird-shaped surveillance drones with advanced AI-enabled perception are a direct challenge to security of India’s northern border. The U.S. Army’s tests of countermeasures against swarms of up to 40 drones simultaneously underline that the battlefield of the future will be contested in three dimensions by machines that think faster than any human controller can react.
Electronic Warfare and the Invisible Front
If drones are the visible face of the cyber-physical battlefield, Electronic Warfare (EW) is its invisible nervous system the domain where signals are jammed, radars are blinded, and GPS coordinates are fabricated. The EW market is forecast to grow from $18.6 billion to $26.6 billion by 2034 (CAGR 5.2%), reflecting massive global investment in electromagnetic dominance.
By 2018, adversaries had mastered GPS spoofing, feeding false coordinates to enemy platforms, causing drones, missiles, or vehicles to navigate to incorrect locations without a single kinetic shot being fired. Pakistan’s locally-developed Spider-AD counter-UAV system, capable of jamming UAV communications and GPS signals at ranges exceeding 10 km, is a direct, present-day threat to India’s own UAV operations along the western border.
Artificial Intelligence: The Brain Behind the Battlefield
Artificial Intelligence is the force-multiplier that transforms individual CPS capabilities into a single, adaptive, learning warfighting system. The AI in modern warfare market is projected to surge from $9.62 billion in 2025 to $28.82 billion by 2034 a CAGR of 12.96%. AI now enables real-time targeting for autonomous weapons, adaptive jamming in EW, predictive maintenance for military platforms, and swarm coordination across hundreds of drones.
The offensive application of AI is equally alarming. Fully autonomous malware now probes and exploits vulnerabilities in both IT and Operational Technology (OT) systems, evolving its approach with minimal human input. Globally, 54% of security leaders identify AI-generated attacks as the biggest cyber risk of 2024-25. During India’s 2024 General Elections, adversaries deployed deepfakes of deceased politicians endorsing candidates a demonstration that cognitive operations are now as much a part of the CPS battlefield as missile guidance.
India’s threat landscape: Nation under siege in cyberspace
India is the world’s 5th most breached nation, 83% of its organisations suffered a cyber incident in 2024, and hostile attacks on government entities surged 138% between 2019 and 2023. The adversary is not waiting.
The numbers tell a story that is both urgent and sobering. India’s rapid digitalization its 970 million internet subscribers, its Aadhaar system serving 1.4 billion identities, its UPI processing billions of daily transactions has created one of the world’s largest attack surfaces, simultaneously a national strength and a national vulnerability (Table2).
Table 2: Cyber-Physical Threat Landscape- Key Statistics (2024–25)
| Metric / Incident | Data / Scale | Source |
| Govt Attacks Cyberattacks on Govt entities (2019 vs 2023) | 85,797 → 2,04,844 — +138% rise | MeitY / Dark Reading |
| Infrastructure DDoS attacks on India’s infrastructure (2024) | +50% year-on-year increase | Positive Technologies |
| Malware Malware detections in India (2025) | 265+ million incidents detected | Seqrite / NewsBytesApp |
| Financial Fraud Cyber fraud losses (2024 alone) | ₹22,845 Cr — 206% rise from 2023 | CERT-In / Drishti IAS |
| Op Sindoor Cyber-attacks during Operation Sindoor (May 2025) | ~2,00,000 hits on power grid; 19-hr DDoS on President’s website | EventusSec / NewsBytesApp |
| APT Groups APT groups targeting India post-Pahalgam (2025) | 7 APT groups; 15 lakh attacks on Critical Information Infrastructure | Maharashtra Cyber / CERT-In |
| Financial Crime Financial losses to cyber criminals (Jan–Apr 2024) | USD 17.6 Billion reported via 7.4 lakh complaints | Stimson Center / NCRP |
| Global Ranking India’s global breach ranking | 5th most breached nation globally | Dark Reading / PG Advisors |
| Org Exposure Organisations reporting ≥1 cyber incident (2024) | 83% of Indian organisations affected | Cloudflare Asia-Pacific Report |
Sources: MeitY, CERT-In, Maharashtra Cyber, Stimson Center, Cloudflare, EventusSec, NewsBytesApp, Dark Reading
Behind these numbers lies a specific, named adversary architecture. China’s Information Support Force reorganized in 2024 from the Strategic Support Force — has dedicated wings conducting Information Warfare against India. The i-Soon leaks of early 2024 provided definitive confirmation: China’s hacking industry has been systematically targeting India’s defence, telecom, and government networks for years. APT groups RedEcho and APT-10 have been specifically linked to attacks on India’s power infrastructure, including the October 2020 Mumbai power outage still the most dramatic demonstration of CPS vulnerability in Indian history, and a glimpse of what a wartime attack could achieve.
Pakistan’s cyber strategy, supplemented by Chinese capabilities and coordination, adds a second front. The APT36 and Side Copy threat groups both Pakistan-linked have been documented in coordinated hybrid warfare campaigns targeting India’s defence and government networks. Their activities during Operation Sindoor in May 2025 including 200,000 power grid intrusion attempts and a 19-hour DDoS on the President’s website confirmed that cyber-physical operations are now fully integrated into Pakistan’s wartime strategy.
India’s financial exposure is equally staggering. Cyber fraud losses hit ₹55644 crore from 2024 alone a 206% jump from 2023. with predictions suggesting losses Cyber frauds in India surged in 2025, with reported losses exceeding ₹22,495 crore ($2.7 billion) from over 28 lakh cases could reach ₹1.2 lakh crore in 2025, equivalent to 0.7% of India’s GDP. This is not just criminal activity it is the financial cost of a nation fighting a cyber war it has not yet fully recognized.
Table 3: Estimated cyber fraud losses in India (2021-25)
Data based on reported financial cyber fraud complaints (TOI, Feb 11, 2026)
| Year | Approx. Reported Complaints | Approx. Reported Financial Loss |
| 2021 | 2.6 Lakh | ₹551 Crore |
| 2022 | 6.9 Lakh | ₹2,290 Crore |
| 2023 | 13.1 Lakh | ₹7,463 Crore |
| 2024 | 19.2 Lakh | ₹22,845 Crore |
| 2025 | 24.0 Lakh (Projected) | ₹22,495 Crore (Jan-Nov) |
| Total | ~65.8 Lakh | ~₹55,644 Crore |
India’s posture: progress, but not enough

The architecture India has built
India has not been ideal; it has made real and commendable progress. The Defence Cyber Agency (DCyA), operationalised in 2021, provides tri-service coordination for joint cyber operations. The 2024 Joint Doctrine for Cyberspace Operations (JDCO) — India’s first official acknowledgement of an offensive military cyber posture — signals a doctrinal shift from passive defence to proactive deterrence. India achieved Tier-1 ranking in the Global Cybersecurity Index a recognition of the maturity of its institutional framework.
Financially, the government has stepped up meaningfully. Cybersecurity allocation has risen from ₹400 crore in 2023-24 to ₹1,900 crore in 2025-26 nearly a five-fold increase in three years. India’s total defence budget for 2025-26 stands at a record ₹6.81 lakh crore a 9.5% increase with dedicated R&D allocation of 3.93% earmarked for technologies including AI and cybersecurity. CERT-In handled over 29.44 lakh cyber incidents in 2025 issuing 1,530 alerts and 65 major advisories a substantial national cyber response capability.
Gaps that cannot be ignored

An honest analysis requires naming the gaps, not just celebrating the gains. Three structural weaknesses define India’s cyber-physical vulnerability:
Talent Deficit: India needs 1.5 million cybersecurity professionals but faces a 30% workforce gap with a shortage of 8 lakh trained professionals, particularly in the high-end disciplines of AI security and OT/ICS protection.
Institutional Fragmentation: The DCyA, CERT-In, NCIIPC, and NTRO remain institutionally siloed, creating coordination delays that adversaries exploit. India still lacks a unified National Cyber Security Strategy with operational command authority.
Legislative Obsolescence: India’s primary cyber legislation the Information Technology Act of 2000 is now 26 years old, predating smartphones, social media, cloud computing, and AI. It is wholly inadequate to govern the cyber-physical battlefield.
Way forward: India’s six-point strategy for the cyber-physical age

India has the talent, the technology base, and the strategic necessity to lead in the cyber-physical domain. What it required is policy clarity with the urgency to act now.
Pillar 1: Create a Unified Cyber-Physical Command (CPC)
The single most impactful institutional reform India can make is the creation of a Unified Cyber-Physical Command a tri-service, cross-ministry body with statutory authority over both military and civilian critical infrastructure cyber defence. This Command must integrate the DCyA, CERT-In, NCIIPC, and NTRO into a single operational architecture, with real-time intelligence fusion and the mandate for both defensive resilience and proportional offensive operations.
The September 2024 amendment empowering the National Security Council Secretariat (NSCS) with cybersecurity coordination authority is the right instinct but coordination is not command. India needs a body with the operational authority to act, not just advise, during a cyber-physical crisis.
Pillar 2: Drive Atmanirbhar Bharat into the CPS Domain
Foreign-sourced components in India’s military CPS chips, sensors, communications modules are potential Trojan horses. The National Cybersecurity Reference Framework 2024 (NCRF) is a useful foundation, but must be implemented with mandatory timelines.
Pillar 3: Build a Cyber-Physical Workforce at War Scale
India must treat its 8-lakh cyber professional deficit as a national emergency comparable in urgency to the nuclear programme. A National Cyber-Physical Defence Academy leveraging India’s network of 23 IITs and NITs should offer specialized curricula in offensive and defensive cyber operations, OT/ICS security, AI warfare, and electronic warfare. A Cyber Territorial Army a reserve corps of private-sector cybersecurity professionals callable in national emergencies would provide India with a surge capacity that no standing force can match.
Pillar 4: Harden Critical Infrastructure with Zero Trust Architecture
Every major sector of India’s economy that relies on networked industrial control systems power, telecom, rail, banking, defence logistics must undergo mandatory CPS security audits and implement Zero Trust Architecture (ZTA) principles: trust nothing, verify everything, assume breach. For OT/ICS environments power plant control systems, water treatment facilities air-gapping from public networks is non-negotiable. The NCIIPC’s periodic CII exercises must become live adversarial simulations, not tick-box compliance events.
India’s planned 52-satellite constellation spanning GEO, MEO, and LEO orbits for military communications is a strategically vital initiative that must be accelerated providing a redundant communications backbone that survives even a Viasat-style attack against commercial satellite networks. This requires clearly enunciated time line backed by funding.
Pillar 5: Articulate a Credible Cyber-Physical Deterrence Doctrine
Strategic ambiguity serves India’s adversaries, not India. Research confirms that India currently lacks credible deterrence-by-punishment capability against China, though it has the potential for deterrence-by-denial if bureaucratic inertia is overcome. India must publish a clear proportional response framework making explicit the costs any adversary will pay for a significant cyber-physical attack on Indian infrastructure. This is not aggression; it is the language adversaries understand. India’s engagement in Quad cyber frameworks and ASEAN cyber dialogues should be deepened, turning India’s non-alignment tradition into a convening authority for international CPS norms the digital-age equivalent of the Geneva Conventions.
Pillar 6: Build a Strategic Communications Command for Cognitive Warfare
The cyber-physical battlefield extends into the minds of citizens and soldiers. Deepfakes, coordinated disinformation, social media manipulation timed to real-world crises these are not peripheral threats; they are central to the adversary’s playbook. India needs a Strategic Communications Command with AI-powered deepfake detection, rapid counter-narrative capability, and a mandate to coordinate with social media platforms during national security crises. The Bharat NCX national cyber exercise must expand its scope from purely technical scenarios to include full-spectrum cognitive warfare simulations. Table 4 summarizes the proposed target/timeline proposed by authors.
Table 4: India’s Strategic Way Forward — Six Pillars of Cyber-Physical Defence
| Strategic Pillar | Key Actions | Target / Timeline |
| 1. Command & Control(Unified Cyber-Physical Command) | Integrate DCyA, CERT-In, NCIIPC and NTRO under one operational body | Establish by 2026–27 |
| 2. Indigenization (Indigenous CPS Capability) | Mandate Indian components in defence systems Expand DRDO / ISRO CPS R&D programs | 50% indigenous by 2030 |
| 3. Talent Pipeline | National Cyber-Physical Defence Academy Cyber Territorial Army Reserve | 0.5 Mn / year intake |
| 4.. Infrastructure Critical Infrastructure Hardening | Zero Trust Architecture deployment Quantum-resistant cryptography Mandatory OT / ICS audit | Phase 1 complete by 2027 |
| 5.Deterrence Credible Deterrence Doctrine | Publish proportional response framework Expand Quad cyber cooperation | White Paper 2026 |
| 6. Cognitive Defence Cognitive Warfare Counter-Strategy | AI deepfake detection systems Strategic Communications Command NCX expansion | Operational by 2026 |
(Author’s Framework)
India’s Moment to Lead or Fall Behind
History rewards those who shape a revolution, not those who merely survive it. The cyber-physical revolution in warfare is underway. India’s choice is either to lead, or to be led.
The cyber-physical battlefield is not an emerging threat it is a conflict India is already engaged, on every front, every day. The 200,000 attacks on India’s power grid during Operation Sindoor; the 15 lakh assaults on critical infrastructure by seven APT groups in the weeks that followed; the ₹22,845 crore lost to cyber fraud in a single year; 83% of Indian organisations suffered a cyber breach in 2024 — these are not statistics. They are battle damage reports from a war that was never formally declared.
India enters this war with genuine strengths. A $3.4 billion cybersecurity ecosystem, one of the world’s largest pools of IT talent, a defence budget of $78.57 billion and growing, world-class space and missile development organisations, and a strategic culture that has navigated far more complex crises. The 2024 Joint Doctrine for Cyberspace Operations signals that India’s military leadership understands the battlefield. The rising budgets signal that the government understands the investment requirement.
What remains is speed the rarest commodity in bureaucratic systems, and the most important in cyber-physical warfare. The adversary does not wait for committee meetings. Algorithms do not observe office hours. The 19-hour DDoS on the President’s website during Operation Sindoor did not pause for a policy review. India must build systems that respond at machine speed, defended by humans who think at strategic depth.
The six pillars outlined in this article are Unified Cyber-Physical Command, indigenous CPS capability, a war-scale talent pipeline, hardened critical infrastructure, credible deterrence, and cognitive warfare defence are not a wish list. They are the minimum viable strategy for a nation that intends to remain sovereign, secure, and strategically autonomous in the age of the cyber-physical battlefield.
India has stood at defining moments in the scenarios in recent times. The cyber-physical frontier is the defining moment of this generation’s strategic leadership. The way forward is mapped. The capability exists. The threat is real. The time to act is now not tomorrow.
While algorithms offer significant advantages, “winning” is complex and often hinges on the integration of technology with strategy and military tradition.

